System Administration Simplified
System administrators (sysadmins) are the unsung heroes ensuring the seamless operation of organizational infrastructures. Mr.Benny is designed to make it easier to juggle complex systems, networks, and applications. Let us see how modern tools and practices help sysadmin work effectively.
What is System Administration anyway?
Managing and maintaining an organization’s IT infrastructure, including servers, networks, user accounts, and software applications is system administration. Sysadmins are tasked with configuring hardware and software, troubleshooting issues, implementing security measures, and ensuring high system availability. Modern sysadmins must now manage cloud-based systems, ensure seamless integration between on-premise and cloud services, and oversee distributed teams and infrastructures.
Automation and responsibilities
Traditionally, sysadmins focused on manual tasks like server setup, network configuration, and hardware maintenance. However, the advent of cloud computing, virtualization, and hybrid IT environments has redefined their role.
By automating repetitive tasks like patch management, user provisioning, and system updates, sysadmins can focus on strategic initiatives rather than mundane operational duties. To simplify complex configurations, sysadmin use tools like
- Ansible: This open-source tool enables configuration management, application deployment, and task automation, offering simplicity and flexibility.
- Puppet: A configuration management tool that automates the provisioning and management of infrastructure, ensuring consistent deployments.
- Chef: An automation platform that treats infrastructure as code, allowing scalable and repeatable configurations.
- PowerShell: A command-line tool and scripting language from Microsoft that facilitates the automation of administrative tasks.
Sysadmin responsibilities include
- Implement Infrastructure as Code (IaC): Managing infrastructure through code enables version control and reduces configuration drift.
- Adopt Monitoring and Logging Solutions: Proactive monitoring and logging help identify and resolve issues before they escalate.
- Utilize CI (Continuos Integration) / CD (Continuos Delivery) Pipelines: Automating the testing and deployment of applications accelerates development cycles and improves agility.
- Remote Work Enablement: Supporting remote teams is now a priority, with sysadmins implementing secure remote access solutions and collaboration tools.
- Zero Trust Security Models: The adoption of zero trust principles redefines network security, emphasizing strict access controls and continuous verification.
MR.BENNY HELPS YOU

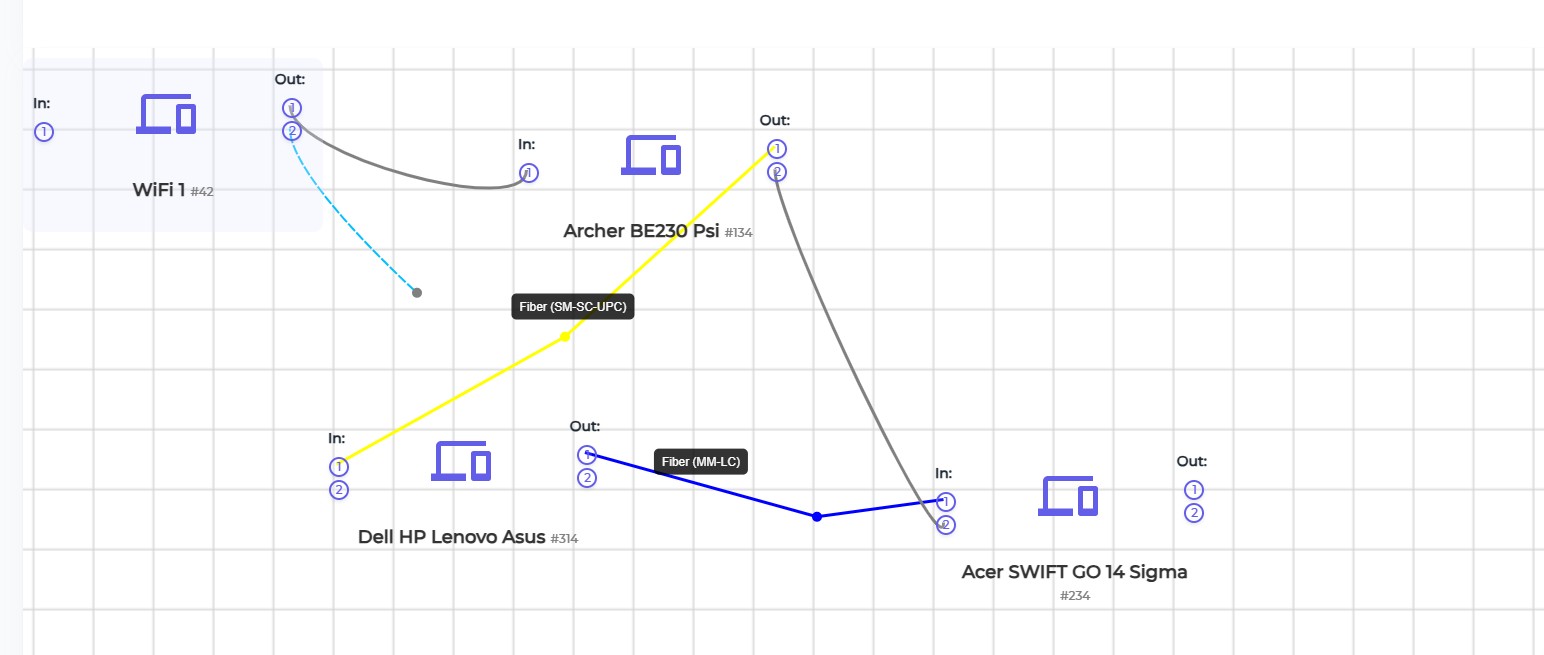
Map visually the position of all the physical assets such as PCs or routers in a room or network
Start Now
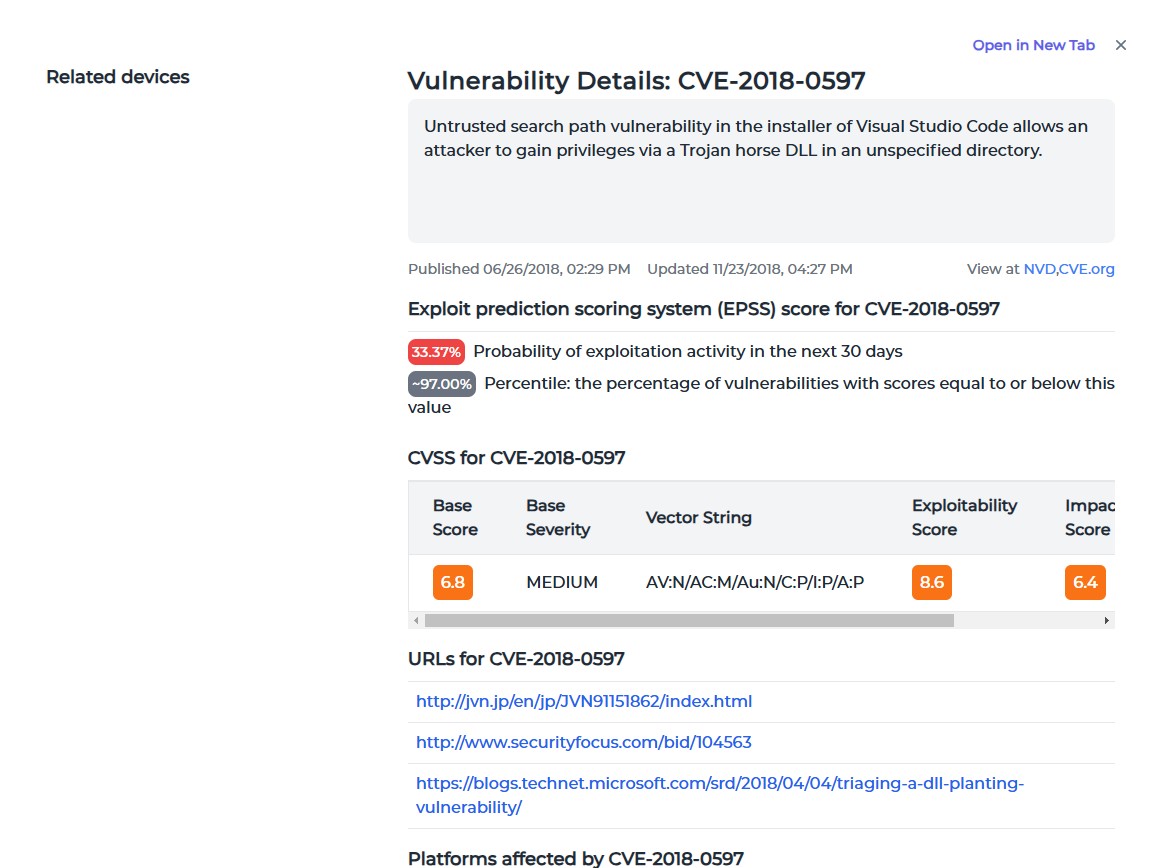
See one vulnerability (CVE) including risk assessment, affected devices, CVSS, EPSS
Start Now
Prepare for the future
Artificial intelligence (AI) is becoming increasingly prominent in cybersecurity, enabling advanced threat detection and response capabilities. It is integrated into Mr.Benny, your smart assistant that provides personalized recommendations to prioritize and how to solve specific tasks required by all your infrastructure elements.
Industry experts agree.
Thomas Vick, Field CTO at Robert Half says “Some of the biggest areasfor AI include automating incident detection, troubleshooting, and enhancing security. It’s not foolproof and doesn’t come without its own glitches, there is a need for ongoing monitoring of AI systems.” (source)
Mark Tauschek, VP of Research Fellowships and Distinguished Analyst at Info-Tech Research says "SysAdmins generally enjoy the work they do, but when there is a disaster or business-impacting event, the pressure to resolve the issue and restore services is intense and very stressful. They are adapting to the influx of AI technologies and the heightened risk of cyber events in the same way most IT professionals are—trying to stay current on what can help them do their jobs."(source)
Embracing automation, adopting best practices, and leveraging our all in one platform, sysadmins can simplify their work and navigate the complexities of modern IT environments.
Do you know there is a free plan available to test?
INSIGHTS
SMALL BUSINESSES
Small businesses just like yours are increasingly becoming targets for cybercriminals. A strategy for cybersecurity is needed. It will ensure operational resilience, customer trust, and legal compliance, forming the backbone of future growth.
Learn moreSYSTEM ADMINISTRATION
System administrators (sysadmins) are the unsung heroes ensuring the seamless operation of organizational infrastructures. Mr.Benny is designed to make it easier to juggle complex systems, networks, and applications. Let us see how modern tools and practices help sysadmin work effectively.
Learn moreITSM SOFTWARE
Many IT managers still rely on Microsoft Excel for various tasks, over 70% to be exact. While Excel offers supreme flexibility, it falls short in handling complex processes, leading to inefficiencies and potential errors. Sooner or later it becomes necessary to replace it with an ITSM solution.
Learn moreNIS-2 COMPLIANCE
Cyber threats are increasingly sophisticated, and the European Union has strengthened its cybersecurity framework through the NIS-2 Directive. Understanding and achieving compliance with NIS-2 is crucial.
Learn moreCVE IMPACT ASSESSMENT
The first line of defense against cybersecurity threats is the Common Vulnerabilities and Exposures (CVE) system, a standardized framework for identifying and cataloging vulnerabilities. With Mr.Benny you stay ahead of evolving threats and get access to CVE databases.
Learn more