CVE Impact Assessment
The first line of defense against cybersecurity threats is the Common Vulnerabilities and Exposures (CVE) system, a standardized framework for identifying and cataloging vulnerabilities. With Mr.Benny you stay ahead of evolving threats and get access to CVE databases.
What is CVE?
The Common Vulnerabilities and Exposures (CVE) system is a global catalog of cybersecurity vulnerabilities in software and hardware. Each CVE entry contains an identifier for a specific vulnerability, providing a standardized reference. Managed by the MITRE Corporation, the CVE system serves as the backbone of modern vulnerability assessment.
CVE Impact Assessment
CVE impact assessments are critical to the cybersecurity strategy, by determining risk exposure. By understanding the severity and potential consequences of vulnerabilities, organizations can prioritize their response, reducing the likelihood of exploitation and minimizing operational disruption. It involves several steps:
- Vulnerability Identification Regular check the CVE database to identify vulnerabilities that may affect your systems
- Severity Analysis Once a vulnerability is identified you have to see how severe it is. The Common Vulnerability Scoring System (CVSS) is used to evaluate the severity of each vulnerability. CVSS scores range from 0.0 to 10.0, with higher scores indicating greater severity. CVSS considers multiple factors, including:
- Attack Vector: The environment through which the vulnerability can be exploited (e.g., network, physical, local).
- Attack Complexity: The level of difficulty an attacker must overcome to exploit the vulnerability.
- Impact Metrics: The potential impact on confidentiality, integrity, and availability.
- Asset Inventory Mapping: In order to assess real security threats based on the vulnerabilities identified is mandatory to keep an up-to-date inventory of IT assets no matter the location of those (hybrid work leads frequently to ignore assets that impact an organization. Mr.Benny provides a comprehensive and visual IT assets management solution organized by room, network or other criteria.
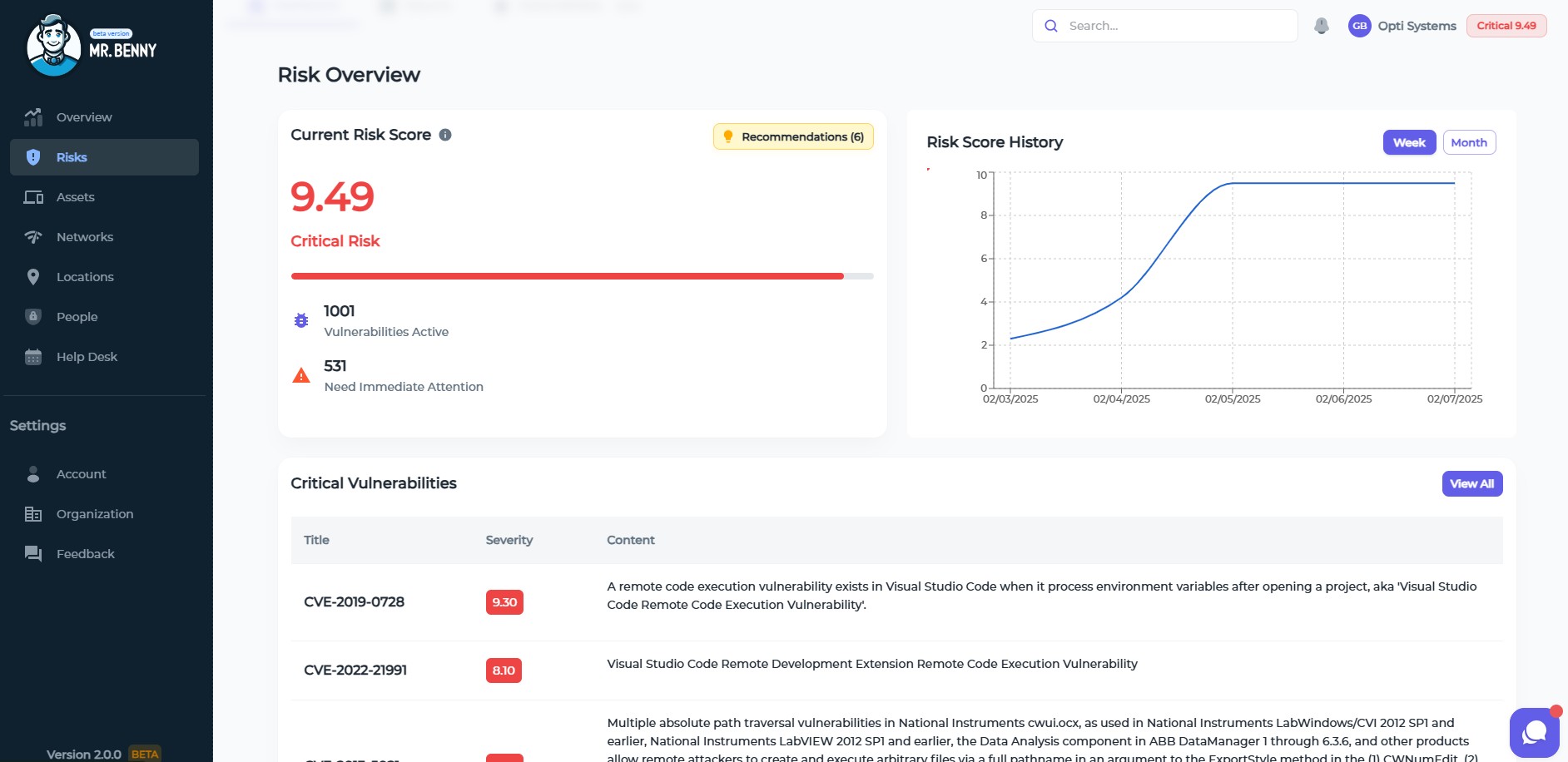
- Risk Assessment By analyzing the criticality of affected assets, data sensitivity, and existing security measures, you can compute the overall risk posed by vulnerabilities or have Mr.Benny do it for you and save your time for more important activities
- Patch Management Ensure timely application of security patches to address patchable vulnerabilities. Mr.Benny as your smart ITAM assistant will provide you not only with prioritization of those security patches, but also with advices how to do it.
- Employee Training Educate staff on cybersecurity to reduce exploitation through human error or miscommunication.
The 3 main reasons why organizations have challenges with the CVE system are:
- High Volume of CVEs With thousands of new CVEs added annually, security teams may struggle to assess and prioritize each vulnerability effectively.
- Dynamic Threat Landscape Threats evolve quickly, and the severity of a vulnerability can change based on new exploits or attack methods.
- Resource LimitationsSmall and medium-sized businesses, in particular, may lack the personnel or technology to perform comprehensive assessments.
MR.BENNY HELPS YOU

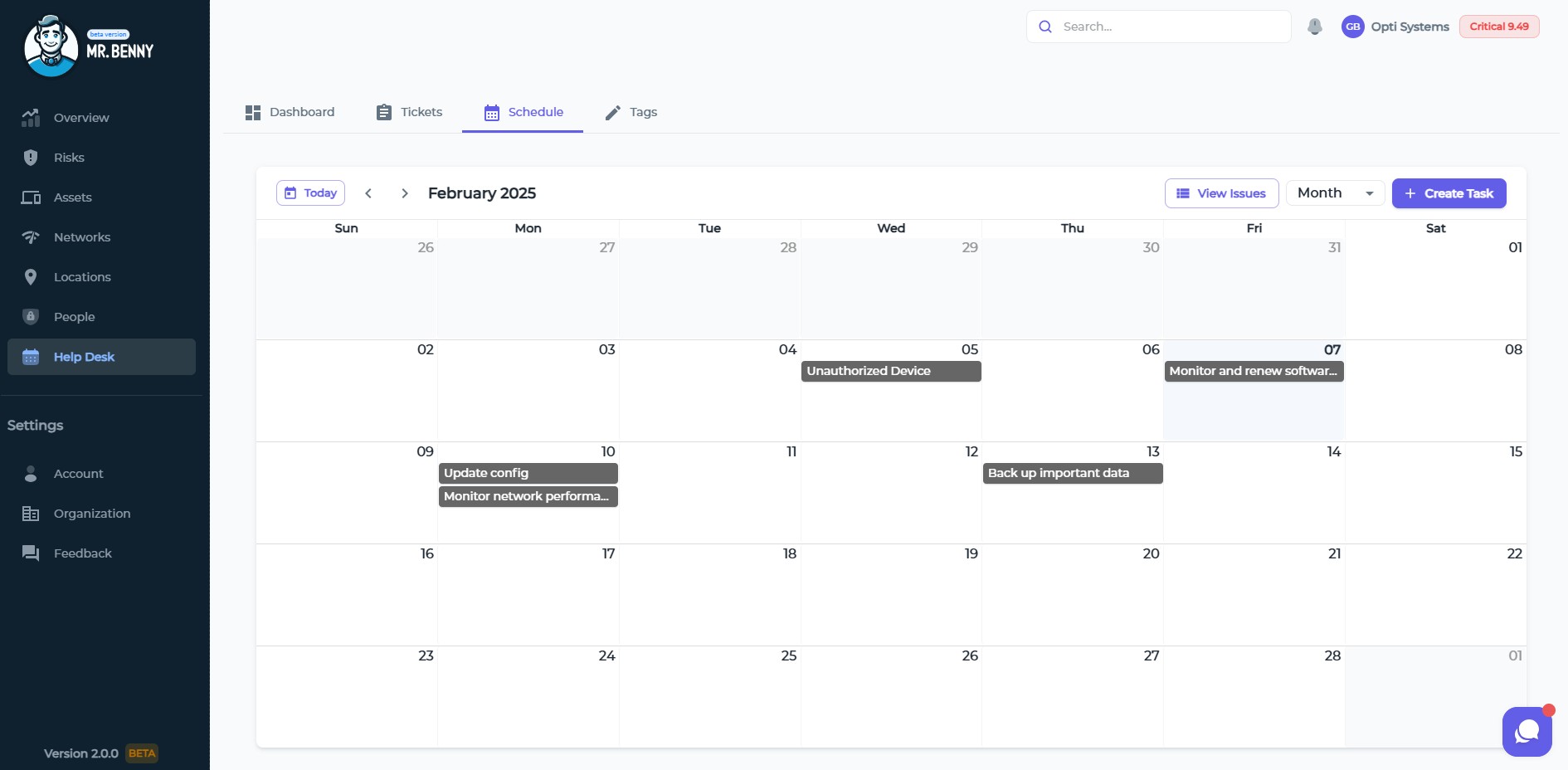
Calendar for all necessary patching and vulnerability checks in your organization
Start Now
Risk score per your entire organization and for each asset, network, location.
Start Now
Prepare for the future
ITSM Software such as Mr.Benny also includes AI and Machine Learning Integration, allowing for proactive issue resolution and improved decision-making regarding vulnerabilities. Automation of tasks and global risk determination will be needed to reduce manual workloads as well. Experts agree.
Ben Edwards, Principal Research Scientist at Bitsight (source)
"With 95% certainty, there will be between 48,675 and 58,956 new CVEs published in 2025, bringing the total to well over 300,000. Prioritization will be key in vulnerability management, emphasizing the importance of threat intelligence."
Peter Barnett, Cybersecurity Analyst at Action1 (source)
"Over 38,000 vulnerabilities were reported in 2024—a sharp increase from previous years. This surge is not just a statistic but a signal: cybercriminals are becoming faster, smarter, and more determined."
Mr.Benny helps with CVE management applied to your IT assets, so you can enhance your security posture, and protect critical assets. We have a free plan available to test, what are you waiting for?
INSIGHTS
SMALL BUSINESSES
Small businesses just like yours are increasingly becoming targets for cybercriminals. A strategy for cybersecurity is needed. It will ensure operational resilience, customer trust, and legal compliance, forming the backbone of future growth.
Learn moreSYSTEM ADMINISTRATION
System administrators (sysadmins) are the unsung heroes ensuring the seamless operation of organizational infrastructures. Mr.Benny is designed to make it easier to juggle complex systems, networks, and applications. Let us see how modern tools and practices help sysadmin work effectively.
Learn moreITSM SOFTWARE
Many IT managers still rely on Microsoft Excel for various tasks, over 70% to be exact. While Excel offers supreme flexibility, it falls short in handling complex processes, leading to inefficiencies and potential errors. Sooner or later it becomes necessary to replace it with an ITSM solution.
Learn moreNIS-2 COMPLIANCE
Cyber threats are increasingly sophisticated, and the European Union has strengthened its cybersecurity framework through the NIS-2 Directive. Understanding and achieving compliance with NIS-2 is crucial.
Learn moreCVE IMPACT ASSESSMENT
The first line of defense against cybersecurity threats is the Common Vulnerabilities and Exposures (CVE) system, a standardized framework for identifying and cataloging vulnerabilities. With Mr.Benny you stay ahead of evolving threats and get access to CVE databases.
Learn more