Navigating NIS-2 Compliance: A Guide for European Organizations
Cyber threats are increasingly sophisticated, and the European Union has strengthened its cybersecurity framework through the NIS-2 Directive. It imposes more stringent requirements on organizations across various sectors. Understanding and achieving compliance with NIS-2 is crucial for businesses aiming to safeguard their operations and maintain trust in the digital landscape.
The NIS-2 Directive, officially Directive (EU) 2022/2555
designed to enhance cybersecurity across the European Union. It builds upon the original NIS Directive by expanding its scope, introducing stricter security requirements, and establishing more rigorous supervisory and enforcement measures. It also aims at a high common level of cybersecurity for network and information systems within the EU, addressing gaps revealed since 2016.
Expanded scope
NIS-2 significantly broadens its applicability compared to the original directive. The initial NIS Directive focused on sectors like energy, transport, and health, NIS-2 includes as well:
- Digital Infrastructure: Internet exchange points, domain name systems, and cloud computing services.
- Manufacturing: Production of critical products such as pharmaceuticals and medical devices.
- Public Administration: Central and regional government entities.
This means that many organizations must now adhere to its requirements. All organizations affected by the directive need to have a clear view of their IT assets with proactive actions to avoid security incidents. This usually represents a mix between IT asset management tools and cybersecurity solutions, that are not always deployed all together. Fortunately Mr.Benny CVE powered all in one platform for IT assets management and cybersecurity is the perfect fit to cover NIS-2 scope.
Enhanced Security Requirements
Mandatory risk management measures include:
- Incident Handling: Establishing robust processes for detecting and responding to security incidents.
- Business Continuity: Developing strategies to maintain essential functions during disruptions.
- Supply Chain Security: Ensuring that third-party providers also comply with cybersecurity standards.
These measures aim to create a resilient infrastructure capable of withstanding and quickly recovering from cyber threats. Additionally, organizations must regularly audit their cybersecurity practices, ensuring alignment with evolving regulatory expectations. Mr.Benny covers all these requirements, as it offers vulnerability management, permission management and a cybersecurity-ready help desk for incident handling.
Reporting Obligations
Timely reporting of cybersecurity incidents is mandated by NIS-2. Organizations are required to:
- Notify Promptly: Report incidents that significantly impact service continuity to the relevant national authorities without undue delay.
- Provide Information: Include specifics about the incident's nature, impact, and mitigation measures taken.
By centralizing incident data, authorities can identify patterns and coordinate cross-border responses to minimize harm.Mr.Benny provides all data needed to prepare the mandatory reports.
Governance and Accountability
NIS-2 also places a strong emphasis on governance for cybersecurity:
- Executive Responsibility: Management bodies are held accountable, ensuring that cybersecurity is a board-level concern.
- Regular Training: Organizations must provide ongoing cybersecurity training, fostering a culture of security awareness.
- Cybersecurity Leadership Roles:Specific roles, such as Chief Information Security Officer (CISO), are designated to oversee implementation and compliance efforts.
NIS-2 aims to ensure that organizations take a proactive stance against cyber threats. The directive emphasizes the importance of cybersecurity as a shared responsibility within the organization. Mr.Benny was created to help with risk visibility and management across an entire small or medium organization, and it aligns with the aim of better governance.
Penalties for Non-Compliance
The penalties are stringent, as is the tradition with EU law:
- Financial Fines: Substantial levies can be imposed, proportionate to the severity of the infringement. Each EU country can define specific range of penalties that can reach up to 10 million Euro or 2% of the last year company turnover
- Reputational Damage: Non-compliance can lead to public disclosure of the breach, which will harm the organization's reputation.
For many businesses, the financial and reputational risks of non-compliance far outweigh the costs of implementing robust cybersecurity measures. Both Mr.Benny plans are really affordable as you can check here.
MR.BENNY HELPS YOU

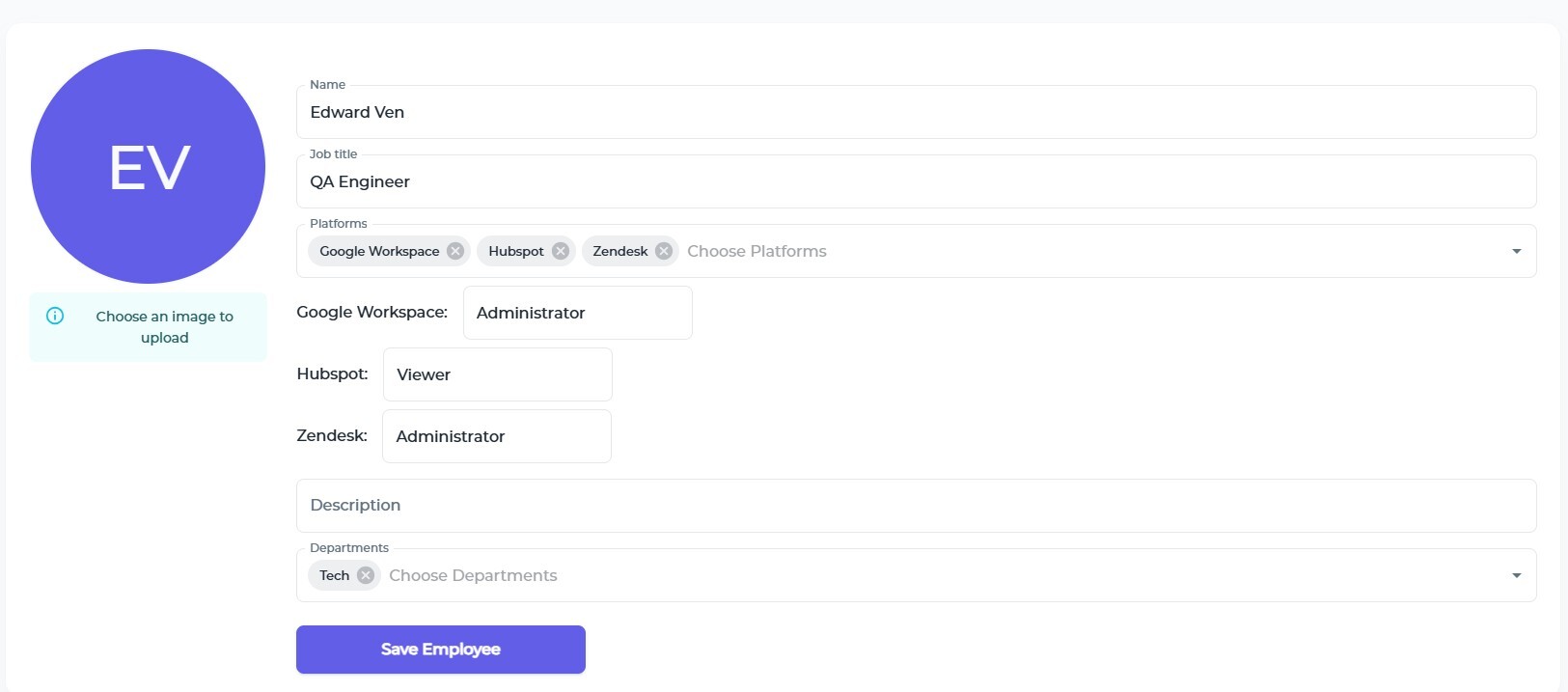
Track the permissions of your employees for each platform, so you can be compliant and avoid permission creep
Start Now
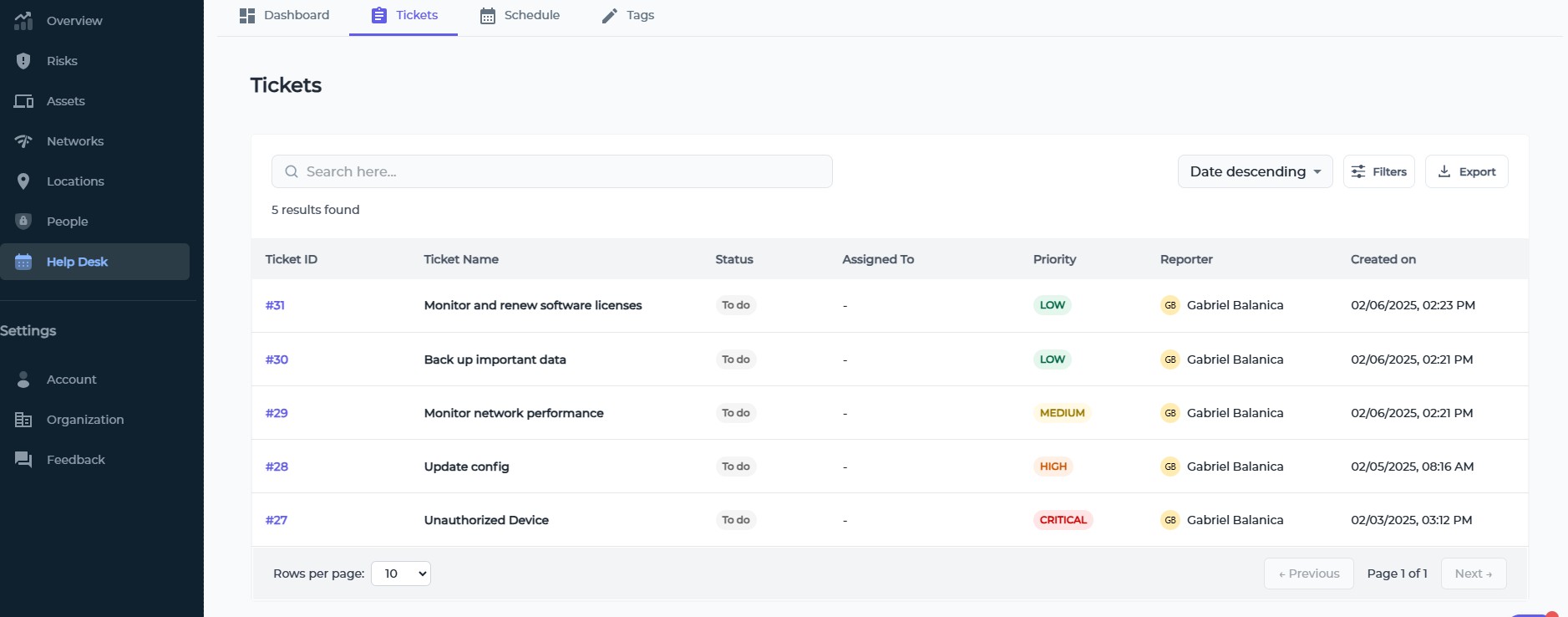
Helpdesk and ticketing module for incident tracking, including patching and vulnerability checks with a calendar
Start Now
Prepare for the future
As the cybersecurity landscape evolves, several trends are anticipated in the context of NIS-2 compliance, such as Increased Regulatory Scrutiny. Authorities are expected to adopt more rigorous supervisory practices to ensure organizations adhere to NIS-2 requirements. Regular audits and assessments will likely become standard practice.
This is the opinion of experts too (source).
Jon France, Chief Information Security Officer at ISC: "NIS2 is bringing things up to date, with the inclusion of a number of additional technologies, such as telecoms, and sectors, all in support of good security outcomes. Its adoption into legislation amongst the various EU member states in the coming months and years will further embed cybersecurity considerations and requirements to the benefit of all EU citizens."
Steve Cottrell, EMEA Chief Technology Officer at Vectra: "Under the previous NIS directive individual states were able to exercise a level of discretion when defining which organizations fell into the category of essential service operators. This led to states adopting and applying different interpretations, which in turn made it difficult to achieve a standard baseline of cyber maturity across the EU. The NIS2 directive directly addresses this as it lays out and details a size cap criterion to ensure medium and large organizations are within scope."
Tools like Mr.Benny play a pivotal role in facilitating NIS-2 compliance journey for now and for the future, offering integrated solutions to manage assets, assess risks, and ensure robust cybersecurity governance.
INSIGHTS
SMALL BUSINESSES
Small businesses just like yours are increasingly becoming targets for cybercriminals. A strategy for cybersecurity is needed. It will ensure operational resilience, customer trust, and legal compliance, forming the backbone of future growth.
Learn moreSYSTEM ADMINISTRATION
System administrators (sysadmins) are the unsung heroes ensuring the seamless operation of organizational infrastructures. Mr.Benny is designed to make it easier to juggle complex systems, networks, and applications. Let us see how modern tools and practices help sysadmin work effectively.
Learn moreITSM SOFTWARE
Many IT managers still rely on Microsoft Excel for various tasks, over 70% to be exact. While Excel offers supreme flexibility, it falls short in handling complex processes, leading to inefficiencies and potential errors. Sooner or later it becomes necessary to replace it with an ITSM solution.
Learn moreNIS-2 COMPLIANCE
Cyber threats are increasingly sophisticated, and the European Union has strengthened its cybersecurity framework through the NIS-2 Directive. Understanding and achieving compliance with NIS-2 is crucial.
Learn moreCVE IMPACT ASSESSMENT
The first line of defense against cybersecurity threats is the Common Vulnerabilities and Exposures (CVE) system, a standardized framework for identifying and cataloging vulnerabilities. With Mr.Benny you stay ahead of evolving threats and get access to CVE databases.
Learn more