A Cybersecurity Strategy for Small Businesses
Small businesses just like yours are increasingly becoming targets for cybercriminals. A strategy for cybersecurity is needed. It will ensure operational resilience, customer trust, and legal compliance, forming the backbone of future growth.
What is Cybersecurity?
Cybersecurity are the technologies designed to protect computers, networks, programs, and data from unauthorized access, attacks, or damage. It ensures the confidentiality, integrity, and availability of sensitive information, safeguarding against threats that could disrupt operations. It consists not only in technical safeguards but also policies, training, and practices that build a resilient defense against evolving threats, even for small businesses.
The Growing Threat Landscape
Small businesses often operate under the misconception that their size makes them less attractive to cybercriminals.
However, statistics tell a different story. Small businesses account for 43% of cyberattacks annually, with the average cost of an attack exceeding $25,000. Threats such as phishing, malware, ransomware, password hacking, and social engineering exploit vulnerabilities inherent in smaller operations, often leaving devastating financial and operational consequences.
Phishing remains one of the most prevalent attacks, targeting employees through deceptive messages designed to steal credentials or install malware.
Malware itself is another common threat, capable of infiltrating systems to extract sensitive data or cause significant operational disruptions.
Ransomware attacks have surged, where attackers encrypt critical business data, demanding payment for its release.
Weak password practices and social engineering tactics further expose businesses, making robust defense measures indispensable.
Best Practices for Enhancing Cybersecurity
Mitigating cybersecurity risks requires implementing a multi-layered defense strategy, including technologies.
- Regular employee training
- Identify phishing attempts
- Maintain strong passwords
- Keeping all software updated
- Access control mechanisms
- Regular data backups to ensure persistence of critical information
- Firewalls, Antivirus and anti-malware solutions
- Advanced network monitoring tools
A Cybersecurity Policy will outline:
- Acceptable use practices for company resources
- Incident response plan with steps to identify, contain, and remediate breaches
- Regular audits of security measures
- Vendor agreements for compliance and the mitigation of risks
These four steps are an essential foundation for a proactive approach to cybersecurity. This translates into a comprehensive inventory of all IT assets (hardware and software) and a risk assessment related to the company inventory. Based on the risk assessment and vulnerabilities identified the business can move to proactive actions and keep an eye on the mandatory updates. All this effort implies resources involved in the Asset Management, Risk Assessment, constant monitoring and updates for the hardware and software. Those resources implies people with specific technical skills and tools or platforms to perform different activities and tasks.
This is how we brought Mr.Benny to life, your smart assistant for managing your IT assets, networks and cybersecurity exposure.
MR.BENNY HELPS YOU

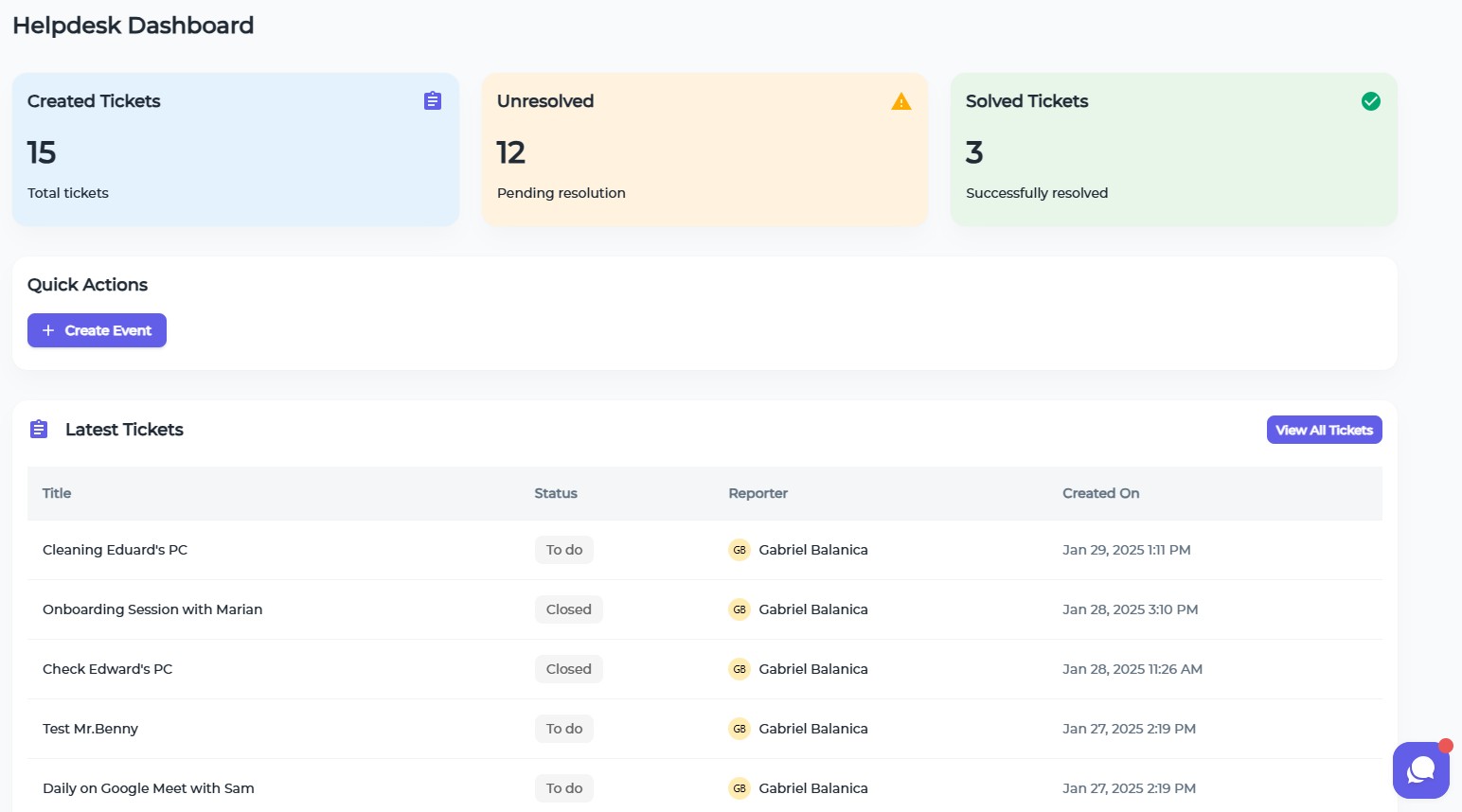
Help desk containing all tasks and tickets related to your assets, security vulnerabilities, including a calendar
Start Now
See and filter all vulnerabilities (CVE) applicable to your hardware and software, including a calendar
Start Now
Prepare for the future
Artificial intelligence (AI) is becoming increasingly prominent in cybersecurity, enabling advanced threat detection and response capabilities. It is integrated into Mr.Benny, providing expert recommendations. At the same time AI makes easier for attacker to perform different type of attacks, and the new open source models that are not at all regulated will lead to an exponential number of attacks on the easiest targets, those that don’t have too many resources to defend - the small business.
Industry experts agree, here are just two voices.
Mallika Sathi, Vice President of Cyber and Intelligence at MasterCard Australia (source).
"Nobody is immune; every business, regardless of size, needs to educate employees. That's a low-cost starting point, but it requires an ongoing investment. It's not just a once and done because the vectors continually change."
Dr. Aastha Gupta, Co-founder of ViCyber (source).
"We have to push our businesses to be more protected because our consumers are protected by our businesses. You’d be surprised how vulnerable some of these businesses are. Manufacturers are targeted for business critical information that is of use to competitors"
Cybersecurity is not a luxury but a necessity for small businesses in today’s digital world. By understanding the risks, implementing best practices, and leveraging advanced technologies like those offered by Mr.Benny, you can build a resilient defense.
We have a free plan available to test, what are you waiting for?
INSIGHTS
SMALL BUSINESSES
Small businesses just like yours are increasingly becoming targets for cybercriminals. A strategy for cybersecurity is needed. It will ensure operational resilience, customer trust, and legal compliance, forming the backbone of future growth.
Learn moreSYSTEM ADMINISTRATION
System administrators (sysadmins) are the unsung heroes ensuring the seamless operation of organizational infrastructures. Mr.Benny is designed to make it easier to juggle complex systems, networks, and applications. Let us see how modern tools and practices help sysadmin work effectively.
Learn moreITSM SOFTWARE
Many IT managers still rely on Microsoft Excel for various tasks, over 70% to be exact. While Excel offers supreme flexibility, it falls short in handling complex processes, leading to inefficiencies and potential errors. Sooner or later it becomes necessary to replace it with an ITSM solution.
Learn moreNIS-2 COMPLIANCE
Cyber threats are increasingly sophisticated, and the European Union has strengthened its cybersecurity framework through the NIS-2 Directive. Understanding and achieving compliance with NIS-2 is crucial.
Learn moreCVE IMPACT ASSESSMENT
The first line of defense against cybersecurity threats is the Common Vulnerabilities and Exposures (CVE) system, a standardized framework for identifying and cataloging vulnerabilities. With Mr.Benny you stay ahead of evolving threats and get access to CVE databases.
Learn more